Have you wondered what’s behind the news about scammers going after a specific six-digit code sent to your mobile device, and then all of a sudden, you find out your account has been hacked, and you have been scammed into spending for something you don’t intend to buy?
With the trend towards adding extra security layers on top of your passwords, these unscrupulous individuals have devised schemes to trick would-be victims into divulging these credentials to access your account. So, what do you need to know about these extra layers of protection, and how can you use it to make your online presence more secure?

Two-factor authentication is a security feature that adds another layer of protection to your account by making it harder for attackers to access a person’s devices or online accounts. Knowing the victim’s password alone is not enough to pass the authentication check.
If a site you use only requires a password to get in and doesn’t offer 2FA, there’s a good chance that it will eventually be hacked. Also, it doesn’t mean that all 2FA has the same level of security. Several types of two-factor authentication are in use today; some may be stronger or more complex than others, but after all, it offers better protection than passwords alone.
SMS Text-Message and Voice-based
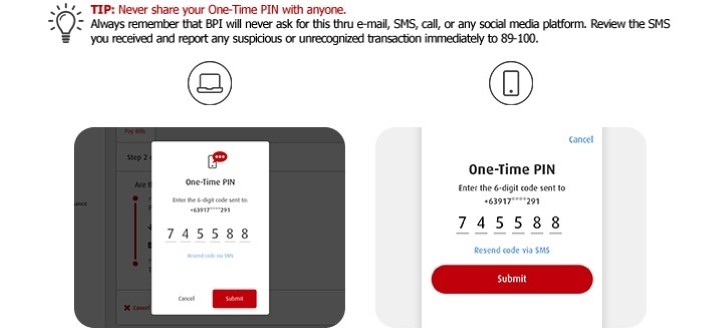
SMS-based 2FA interacts directly with your phone. After receiving a username and password, the site sends the user a unique one-time passcode (OTP) via text message. However, SMS is considered to be the least secure way to authenticate users. Because of this, many companies upgrade their security by moving beyond SMS-based 2FA or warning you not to share the OTP whomever as possible.
Hardware Tokens
The oldest form of 2FA, it produces a new numeric code in a specific second. When users try to access an account, they glance at the device and enter the displayed 2FA code back into the site or app.
Software Tokens
Apple iOS, Google Android, and Windows 10 all have apps that support 2FA, enabling the phone to serve as the physical device to satisfy the possession factor. Authenticator apps replace the need to obtain a verification code via text, voice call, or email. A user must download and install a 2FA app on their smartphone or desktop. They can then use the app with any site that supports this type of authentication.
Push Notification
It’s passwordless authentication with no codes to enter, and no additional interaction is required. It verifies the user by sending a notification directly to a secure app on the user’s device, alerting the user that an authentication attempt is happening. The user can view the authentication attempt’s details and either approve or deny access with a single tap. If the user agrees with the authentication request, the server receives that request and logs it into the web app.
Biometrics
Another passwordless authentication where in recent innovations include verifying a person’s identity via fingerprints, retina patterns, and facial recognition. It is commonly used now on online banking.
If you want to know how to activate your 2FA in your different accounts, we have a separate guide for that. Check it out here.
Two-factor authentication is one way to secure your accounts against unauthorized access, but we must remember that it is not the ultimate solution to safeguard our online accounts. It is one layer of protection that can give us peace of mind. Still, we must remember that using strong passwords, changing these regularly, and vigilant with our browsing habits will protect us from scammers and hackers who seek benefit at our expense.

YugaTech.com is the largest and longest-running technology site in the Philippines. Originally established in October 2002, the site was transformed into a full-fledged technology platform in 2005.
How to transfer, withdraw money from PayPal to GCash
Prices of Starlink satellite in the Philippines
Install Google GBox to Huawei smartphones
Pag-IBIG MP2 online application
How to check PhilHealth contributions online
How to find your SIM card serial number
Globe, PLDT, Converge, Sky: Unli fiber internet plans compared
10 biggest games in the Google Play Store
LTO periodic medical exam for 10-year licenses
Netflix codes to unlock hidden TV shows, movies
Apple, Asus, Cherry Mobile, Huawei, LG, Nokia, Oppo, Samsung, Sony, Vivo, Xiaomi, Lenovo, Infinix Mobile, Pocophone, Honor, iPhone, OnePlus, Tecno, Realme, HTC, Gionee, Kata, IQ00, Redmi, Razer, CloudFone, Motorola, Panasonic, TCL, Wiko
Best Android smartphones between PHP 20,000 - 25,000
Smartphones under PHP 10,000 in the Philippines
Smartphones under PHP 12K Philippines
Best smartphones for kids under PHP 7,000
Smartphones under PHP 15,000 in the Philippines
Best Android smartphones between PHP 15,000 - 20,000
Smartphones under PHP 20,000 in the Philippines
Most affordable 5G phones in the Philippines under PHP 20K
5G smartphones in the Philippines under PHP 16K
Smartphone pricelist Philippines 2024
Smartphone pricelist Philippines 2023
Smartphone pricelist Philippines 2022
Smartphone pricelist Philippines 2021
Smartphone pricelist Philippines 2020